Get prepared for a facepalm: 90% of credit card readers now use the exact password.
The passcode, set by default on credit rating card equipment due to the fact 1990, is very easily found with a speedy Google searach and has been uncovered for so long there’s no sense in attempting to conceal it. It is both 166816 or Z66816, depending on the device.
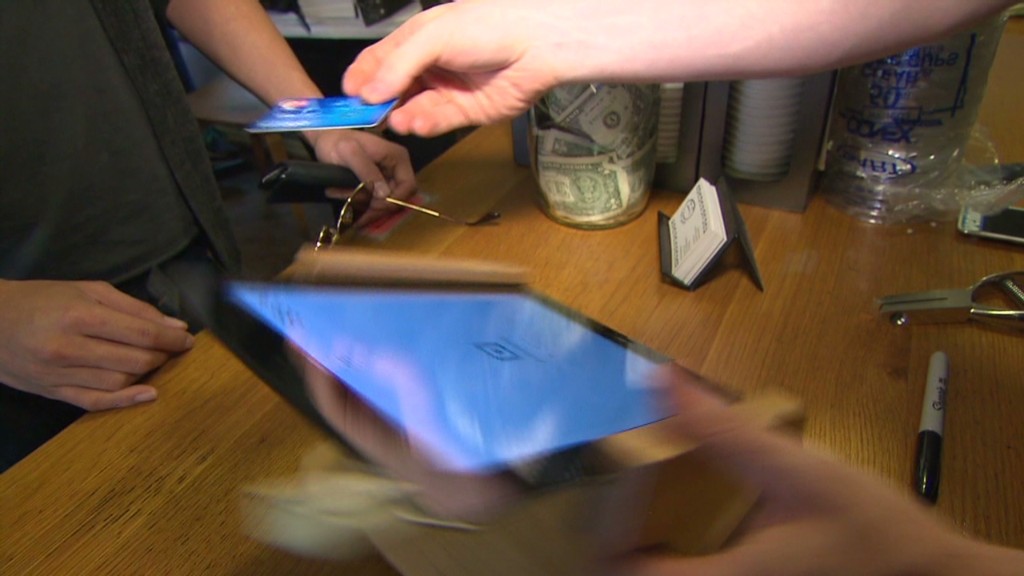
With that, an attacker can gain complete handle of a store’s credit rating card audience, most likely allowing for them to hack into the devices and steal customers’ payment information (believe the Concentrate on (TGT) and Residence Depot (Hd) hacks all around once more). No speculate large vendors preserve shedding your credit history card data to hackers. Security is a joke.
This most current discovery will come from researchers at Trustwave, a cybersecurity firm.
Administrative obtain can be employed to infect machines with malware that steals credit score card information, discussed Trustwave govt Charles Henderson. He detailed his conclusions at very last week’s RSA cybersecurity conference in San Francisco at a presentation named “That Level of Sale is a PoS.”
Choose this CNN quiz — find out what hackers know about you
The issue stems from a activity of warm potato. Device makers promote equipment to exclusive distributors. These suppliers provide them to retailers. But no one thinks it is their task to update the grasp code, Henderson instructed CNNMoney.
“No a person is transforming the password when they set this up for the first time every person thinks the safety of their place-of-sale is someone else’s obligation,” Henderson said. “We are creating it really simple for criminals.”
Trustwave examined the credit history card terminals at far more than 120 retailers nationwide. That consists of big clothing and electronics retailers, as well as nearby retail chains. No precise suppliers were being named.
The wide majority of devices had been made by Verifone (Spend). But the exact concern is current for all big terminal makers, Trustwave said.

A spokesman for Verifone explained that a password alone is not enough to infect devices with malware. The enterprise reported, until finally now, it “has not witnessed any attacks on the safety of its terminals centered on default passwords.”
Just in scenario, nevertheless, Verifone claimed suppliers are “strongly encouraged to alter the default password.” And currently, new Verifone units occur with a password that expires.
In any circumstance, the fault lies with suppliers and their special sellers. It is like property Wi-Fi. If you get a house Wi-Fi router, it is up to you to change the default passcode. Stores really should be securing their possess devices. And equipment resellers should be encouraging them do it.
Trustwave, which helps guard suppliers from hackers, stated that preserving credit rating card equipment secure is minimal on a store’s list of priorities.
“Corporations expend extra dollars selecting the coloration of the level-of-sale than securing it,” Henderson claimed.
This dilemma reinforces the summary created in a recent Verizon cybersecurity report: that merchants get hacked mainly because they’re lazy.
The default password point is a severe challenge. Retail computer system networks get uncovered to pc viruses all the time. Look at 1 scenario Henderson investigated lately. A horrible keystroke-logging spy software ended up on the pc a store takes advantage of to system credit rating card transactions. It turns out staff experienced rigged it to play a pirated model of Guitar Hero, and accidentally downloaded the malware.
“It exhibits you the amount of access that a large amount of folks have to the point-of-sale natural environment,” he mentioned. “Frankly, it really is not as locked down as it really should be.”
CNNMoney (San Francisco) Very first posted April 29, 2015: 9:07 AM ET